Signal is working on a standalone version of its desktop app that does not require a smartphone. Signal Desktop will also gain additional options when used as a linked device.
Signal’s end to end encrypted, yes… But we do the key exchange process through Signal’s servers, don’t we? How do we know they don’t store copies of the keys? Does the client have a mechanism in place to make sure the man in the middle doesn’t do anything funny? I haven’t actually delved very deep into the code, but it sounds like I should.
And… Sure, their server code may be open source too, but nobody guarantees that that’s the code actually running on their servers.
How do we know they don’t store copies of the keys?
I don’t know how Signal is built, but you can establish a secure communication channel through a channel that’s being listened in on, meaning the server doesn’t need to ever see the keys. Look up Diffie-Hellman for an example, an algorithm that lets two actors establish a shared secret without communicating enough information to reconstruct the secret.
So if the client uses a secure key exchange algorithm (or straight up asymmetrical encryption) the server can’t just grab your keys - you just need a secure way to verify that your keys actually match, because what they could do is a man in the middle attack where they establish a secure channel with you and the person you’re messaging, and decrypt and reencrypt messages going both ways, being able to listen in and modify messages.
Here is an overview of all audits done on Signal: https://community.signalusers.org/t/overview-of-third-party-security-audits/13243
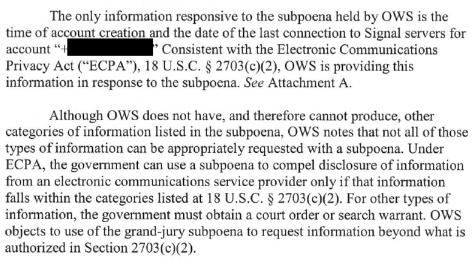
No recent server audits really. They are pretty public about information requests made by the government and their responses though, and from what I can see the only pieces of information they have shared with the government to this point are the time of account creation and the date of the last connection to Signal servers:
You can check more of their responses from here: https://signal.org/bigbrother/
You know, I’ve been thinking…
Signal’s end to end encrypted, yes… But we do the key exchange process through Signal’s servers, don’t we? How do we know they don’t store copies of the keys? Does the client have a mechanism in place to make sure the man in the middle doesn’t do anything funny? I haven’t actually delved very deep into the code, but it sounds like I should.
And… Sure, their server code may be open source too, but nobody guarantees that that’s the code actually running on their servers.
I don’t know how Signal is built, but you can establish a secure communication channel through a channel that’s being listened in on, meaning the server doesn’t need to ever see the keys. Look up Diffie-Hellman for an example, an algorithm that lets two actors establish a shared secret without communicating enough information to reconstruct the secret.
So if the client uses a secure key exchange algorithm (or straight up asymmetrical encryption) the server can’t just grab your keys - you just need a secure way to verify that your keys actually match, because what they could do is a man in the middle attack where they establish a secure channel with you and the person you’re messaging, and decrypt and reencrypt messages going both ways, being able to listen in and modify messages.
They ship their all with blobs, so we cannot verify what their app is doing.
Here is an overview of all audits done on Signal:
https://community.signalusers.org/t/overview-of-third-party-security-audits/13243
No recent server audits really. They are pretty public about information requests made by the government and their responses though, and from what I can see the only pieces of information they have shared with the government to this point are the time of account creation and the date of the last connection to Signal servers:
You can check more of their responses from here:
https://signal.org/bigbrother/